Despite the fact that Web3 has built powerful tools and infrastructure, the average internet user still lives in Web2.
Written by: Figo @IOSG
Introduction
Cryptocurrency has come a long way. Layer 2 scaling solutions are live, zkVMs have emerged, and even ETFs have been approved. However, most people still feel that the blockchain space is an isolated world — something they have only read about in text but have not actually used.
Why is this the case?
The answer lies not in the technology itself, but in what it currently cannot touch: our digital lives. Although Web3 has built powerful tools and infrastructure, the average internet user still lives in Web2 — browsing, trading, and socializing on centralized platforms that control their data.
Mainstream adoption remains elusive until we can connect these two worlds in a trustless, privacy-preserving manner.
Why Web3 has not yet broken through
We often interact online — through banks, social media, streaming platforms, and government portals. But all of this happens within tightly controlled ecosystems. Our digital identities are fragmented across various platforms, each holding a part of our lives: bank statements here, passport scans there, and work history on LinkedIn.
This fragmentation brings two fundamental issues:
Data silos: Your online identity is scattered across platforms, each with its own rules and permissions.
Lack of ownership: You do not actually own your data. At best, you have access — which can be revoked, restricted, or monetized at will by others.
These issues manifest in the friction we face daily. Want to prove your income? You may need to hand over a complete bank statement. Need to verify your address? Be prepared to upload an entire utility bill. These systems assume that complete transparency is the only way to build trust, as there is no infrastructure for selective, verifiable disclosure.
Web3 promises to empower users with control, but so far, it has not delivered on this promise — at least not for everyday, Web2-derived data.
The missing piece: Verifiable Web2 data
This is the real bottleneck: enabling Web3 applications to leverage the data we have already generated — without compromising user privacy or introducing new trusted intermediaries.
There are two key challenges:
Verifiability: How can we cryptographically prove that data from Web2 sources is trustworthy without relying on centralized oracles or APIs?
Privacy: How can we prove only what is necessary — without exposing the complete underlying data?
Chainlink and other oracle providers have addressed some verifiability issues, particularly for public data, such as asset prices or weather conditions. However, personal, user-specific data — such as financial records, qualifications, and identity credentials — requires a different approach. These data points exist behind logins and encrypted channels, and they are not designed to be extracted or shared.
This is where zkTLS comes into play.
What is zkTLS?
Most of the internet runs on TLS (Transport Layer Security) — the encryption protocol that supports HTTPS. It protects about 95% of web traffic. When you visit a website, TLS ensures that your communication is encrypted and cannot be tampered with.
zkTLS (Zero-Knowledge TLS) builds on this foundation with some entirely new capabilities: it allows users to extract and prove specific facts from Web2 data streams without revealing the full content and without trusting third parties.
This unlocks two key capabilities:
On-chain verifiability: zkTLS can prove that data comes from a specific Web2 source and has not been tampered with.
Selective disclosure: It can prove specific attributes — such as "my annual income exceeds $80,000" — without revealing the actual bank statement.
How does it work? Simply put:
It captures the encrypted TLS session between the user and the website.
It generates a zero-knowledge proof that verifies a specific claim (e.g., that a certain value appears in the response).
This proof can then be verified on-chain — trustlessly and privately.
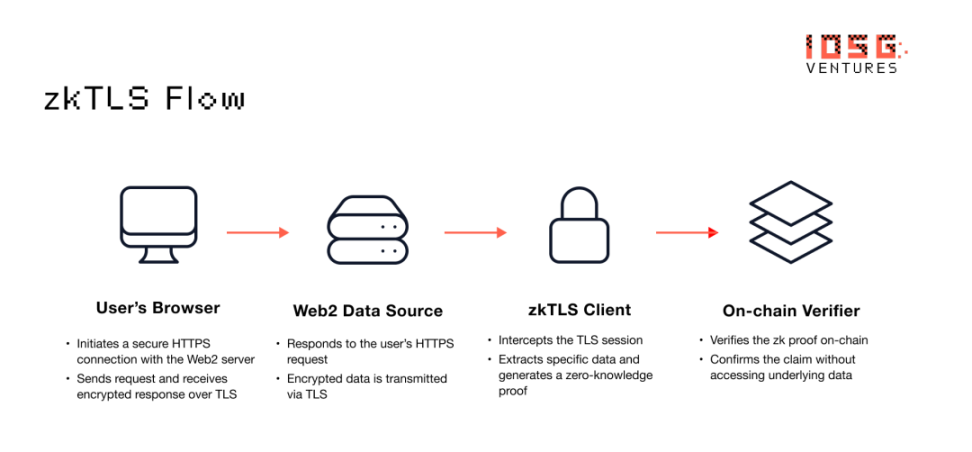
▲ Source: IOSG Ventures
This eliminates the need to expose data to third parties or trust centralized servers to prove the data. Instead, trust is embedded in the cryptographic proof itself.
This is not just theoretical. Implementations of zkTLS have already been tested and deployed in consumer and DeFi use cases, signaling that verifiable Web2 data will become the default input for Web3 applications.
How zkTLS works
Not all zkTLS implementations are the same. Depending on the most important factors — speed, decentralization, or simplicity — different approaches excel in different contexts. Here are three common architectures:
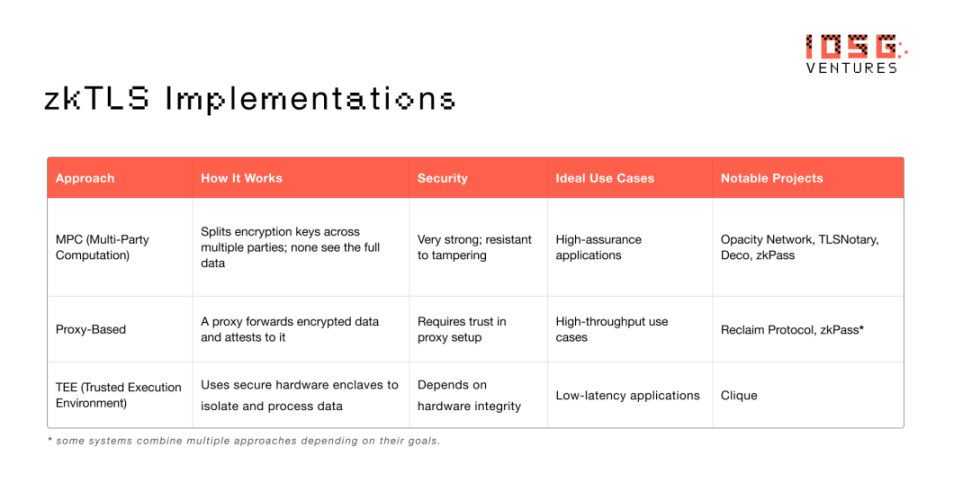
▲ Source: IOSG Ventures
Real-world applications: Where zkTLS changes everything
zkTLS not only optimizes data processing — it also redefines the boundaries between Web2 and Web3. By implementing trust-minimized, private access to off-chain data, it allows applications to integrate real-world context without compromising privacy or decentralization.
Here are the ways it is currently being applied across different domains.
Financial Services
Due to a lack of trusted identity and on-chain financial data, most DeFi protocols still rely on over-collateralization. zkTLS makes it possible to verify income, cash flow, or account history — without exposing sensitive documents.
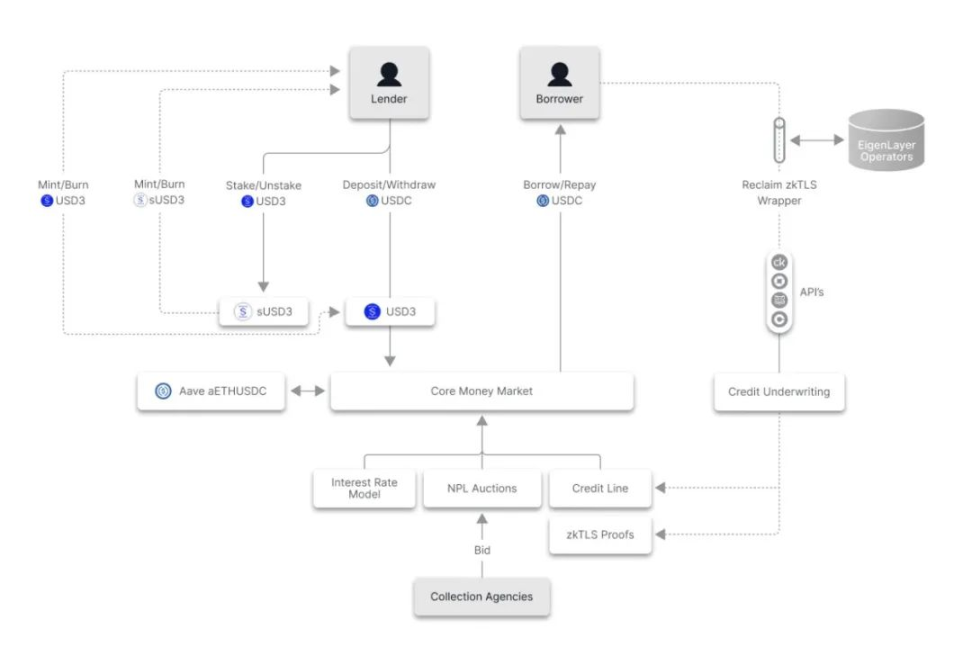
▲ Source: 3Jane
3Jane (3jane.xyz) is building a peer-to-pool credit protocol that provides real-time, unsecured USDC credit lines for traders, farmers, and businesses. Borrowers connect their wallets and Web2 financial data through Plaid, unlocking credit based on verifiable proofs from DeFi, CEX, and banks — without collateral.
Stormbit (stormbit.finance) supports a flexible peer-to-peer lending market where borrowers can privately prove income or account activity, unlocking funds using zkTLS.
RWA (Real World Assets) tokenization projects are beginning to use zkTLS to verify land or property ownership through government portals, achieving compliant on-chain assetization.
zkP2P (zkp2p.xyz) is building a decentralized fiat-to-crypto gateway that allows users to prove payments from Venmo, Wise, or Revolut using zkTLS — without KYC, without intermediaries, and with instant settlement.
These systems expand access to capital, bring credit value on-chain, and establish compliant bridges between TradFi and crypto.
Consumer Platforms
In Web2, access to digital goods, subscriptions, and purchase history is locked behind centralized APIs. zkTLS makes this data portable and provable — without needing permission from the platform.
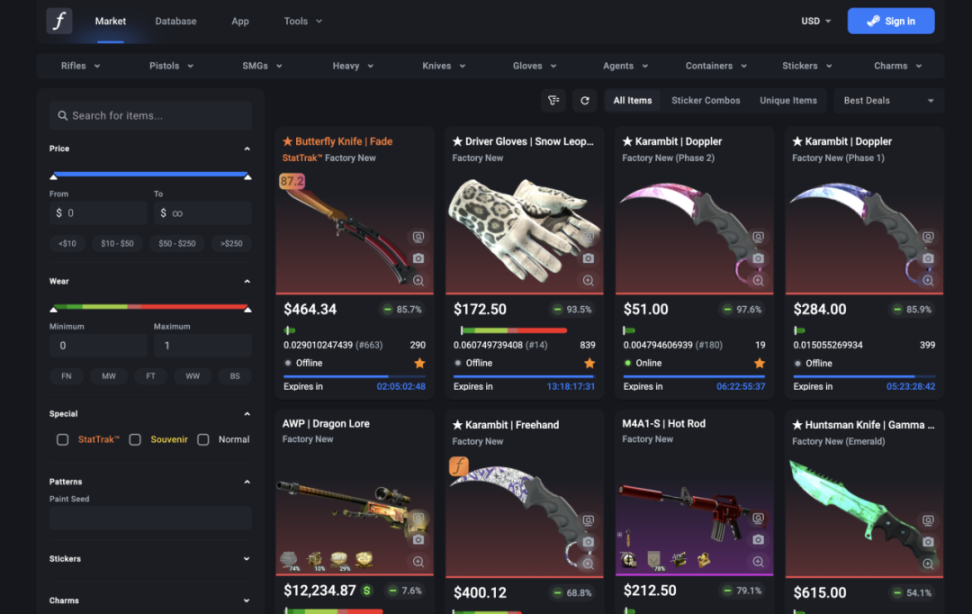
▲ Source: CSFloat
CSFloat (csfloat.com) allows users to verify ownership of Counter-Strike skins and collectibles through Steam data, enabling secure peer-to-peer transactions without platform intervention.
zkTLS is also used to prove access to closed communities, subscriptions, or premium content — without account linking or API access.
In e-commerce, users can prove past purchases or loyalty program activities to unlock cashback, token rewards, or resale markets.
Now imagine proving you own a Spotify subscription — or a luxury brand purchase — without exposing your full account. That is the power of zkTLS.
Identity and Reputation
Today's digital identities are fragmented and overly exposed. Proving your identity often means sharing everything. zkTLS changes this by allowing selective disclosure from trusted sources.
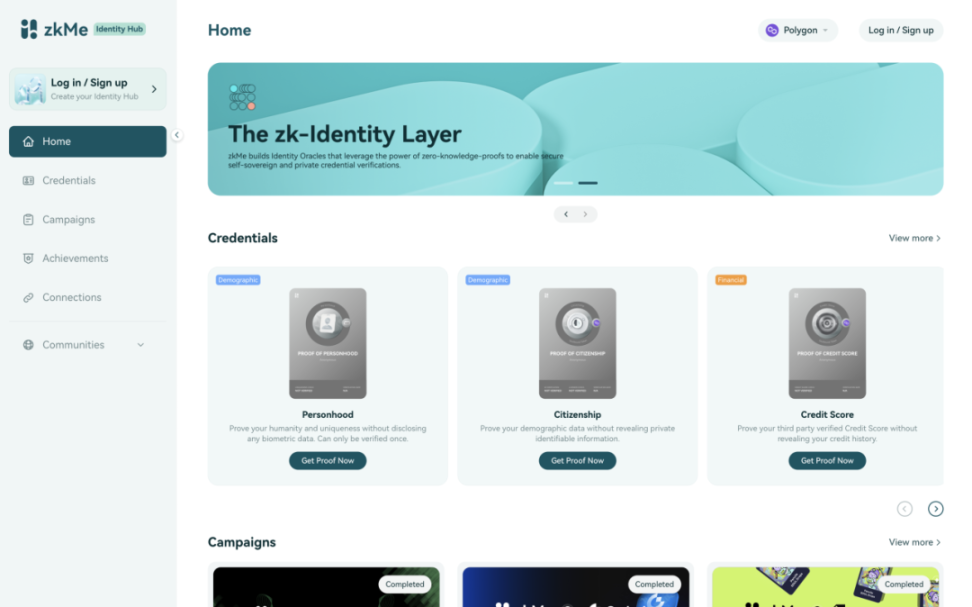
▲ Source: zkMe
zkMe (zk.me) acts as a privacy-preserving identity oracle, transforming documents and data from Web2 platforms into selective on-chain proofs.
Zeru (zeru.finance) supports zScore, a cross-application reputation layer on Base. It verifies credit scores, locations, or Uber histories — without KYC — allowing users to build verifiable profiles for use across applications and ecosystems.
Icebreaker (icebreaker.xyz) enables professionals to create trusted, verifiable work profiles based on employment history and social graphs.
Now imagine someone building a Web3 version of Uber or DoorDash. Drivers show up with zkTLS-verified credentials — no onboarding friction, no need to rebuild reputation.
Social and Content
The content we watch, play, and interact with says a lot — but this data is trapped on platforms. zkTLS unlocks this data, making participation portable and programmable.
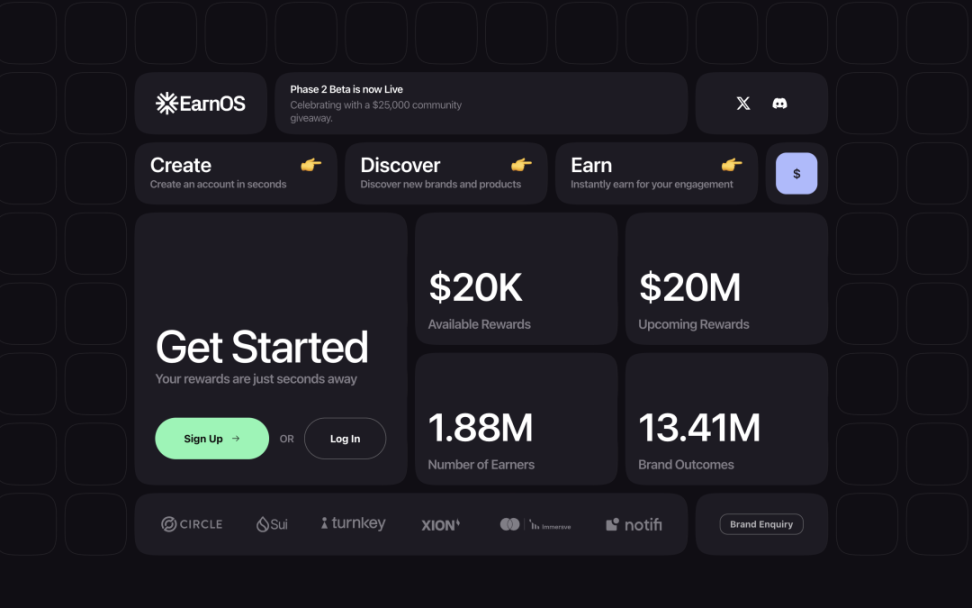
▲ Source: EarnOS
EarnOS (earnos.com) allows users to prove they have viewed or interacted with advertisements — without revealing who they are. Advertisers reach real people, users earn rewards, and data remains private.
Showdown (showdown.win) uses zkTLS through FACEIT to verify gaming profiles and performance data. Players can prove their skills and claim game-based rewards — without screenshots.
This unlocks the next wave of attention markets and participation-driven rewards — ultimately cross-platform portable.
Impact and Behavior
Behavioral systems — whether for fitness, sustainability, or rewards — often require private and hard-to-verify data. zkTLS makes it possible to prove actions without being monitored.
Daylight (https://linktr.ee/godaylight) uses IoT and registered data to verify ownership and usage of solar panels — without exposing user identity or location.
Fit Club (x.com/fitclubonbase) links exercise rewards to verified Strava activities without leaking health or GPS data.
Other applications are exploring the use of zkTLS to prove public transport usage, recycling, or participation in environmental projects — achieving transparent, privacy-preserving incentive systems.
With zkTLS, we can finally prove real-world actions — without being monitored.
Emerging Frontiers
At the edge of artificial intelligence, agency, and decentralized coordination, zkTLS provides critical infrastructure for proof and trust.
ElizaOS (elizaos.ai) is building autonomous agents that generate zk-supported logs of their actions — making AI decision-making verifiable and auditable.
Ketl (ketl.xyz) enables whistleblowers and experts to prove affiliations or insights without exposing their identities — bringing credibility to anonymous communication.
zkTLS is also used to verify training data for machine learning — ensuring authenticity while protecting contributor privacy.
As agents and AI become more autonomous, zkTLS anchors them in fact.
From Credentials to Ownership
zkTLS not only makes Web2 data available in Web3 — it also makes it ownable. Credentials that were once isolated on platforms become portable, programmable, and privacy-preserving.
As more applications adopt zkTLS, we will see a compounding effect: more verifiable data leads to more powerful applications, empowering users with greater control — and more reasons to unlock data on their own terms.
This is not about replacing existing systems. It is about empowering users with control over them — and building a path where trust, privacy, and composability expand together.
The Road Ahead
If crypto wants to go mainstream, it needs to meet users where they already are on the internet. zkTLS provides the infrastructure to achieve this goal.
It enables:
Cryptographic trust in data from Web2 services
Privacy-preserving verification without third parties
A user-controlled composable identity layer
New types of applications based on verifiable real-world interactions
As more of our online lives become accessible through verifiable claims, a new generation of applications will emerge — applications that empower users with greater control, reduce friction, and unlock real value. zkTLS is not just another protocol — it is a new way of thinking about how information moves between platforms and how trust is built on the internet.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




