Author: SlowMist Security Team
Overview
In November 2024, the total loss from Web3 security incidents was approximately $86.24 million. Among these, according to the SlowMist Blockchain Hacked Archive (https://hacked.slowmist.io), there were 21 hacking incidents resulting in losses of about $76.86 million, with $25.5 million recovered. The causes of these incidents included contract vulnerabilities, account hacks, and price manipulation. Additionally, according to the Web3 anti-fraud platform Scam Sniffer, there were 9,208 phishing incident victims this month, with losses amounting to $9.38 million.
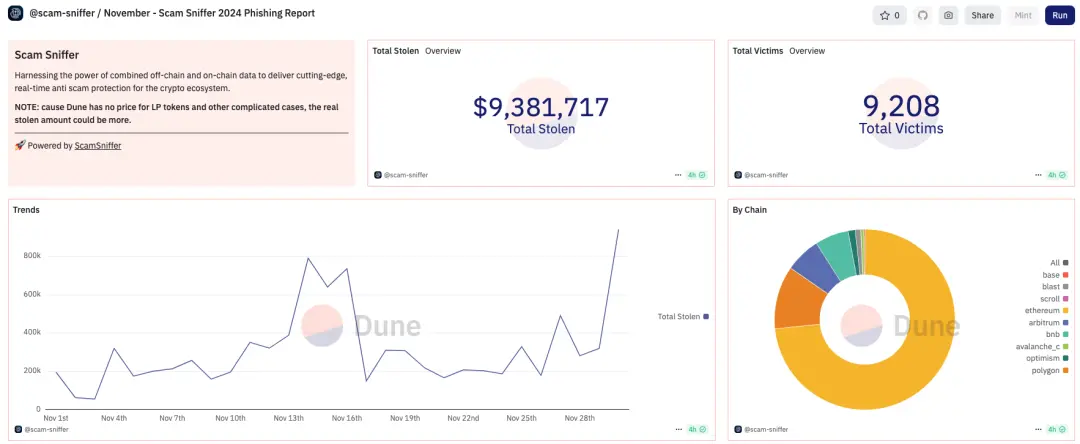
(https://dune.com/scam-sniffer/november-scam-sniffer-2024-phishing-report)
Major Security Incidents
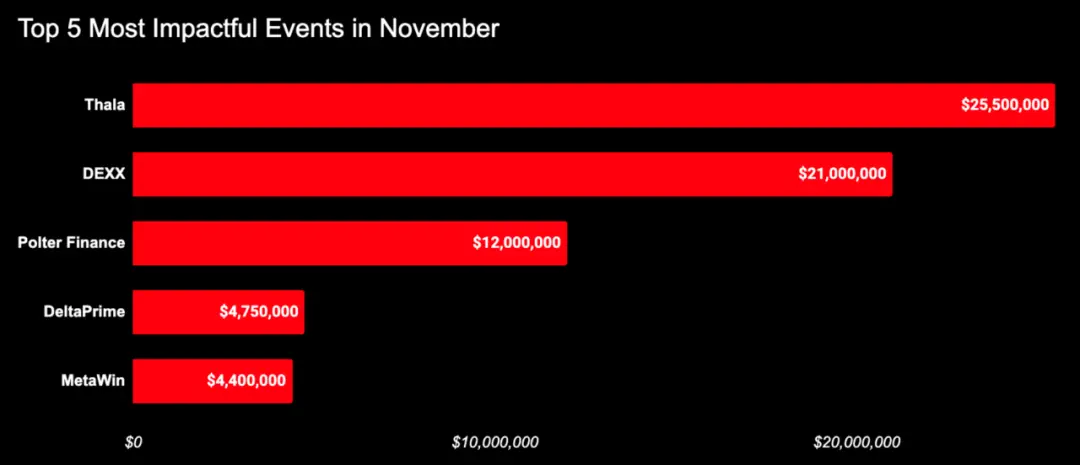
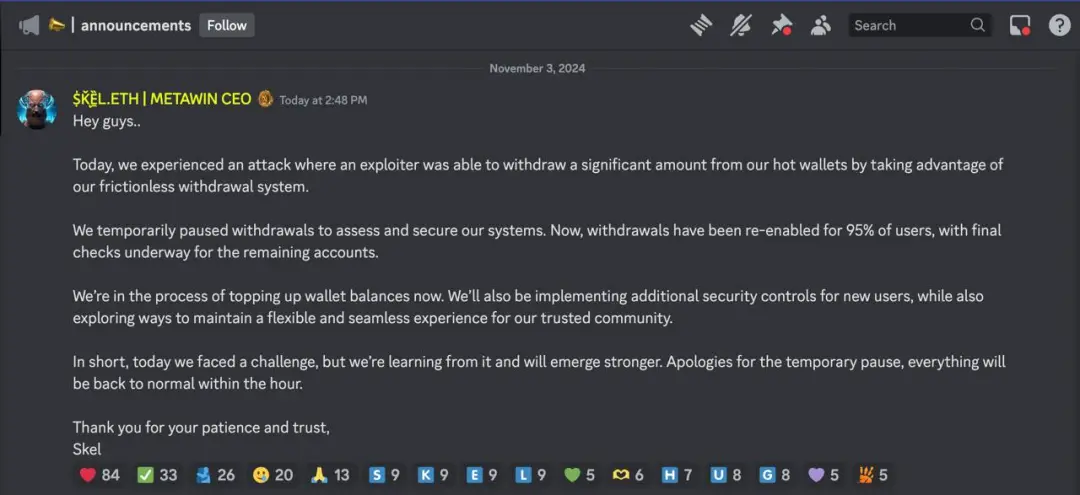
MetaWin
On November 4, 2024, on-chain detective ZachXBT reported that the crypto gambling platform MetaWin was allegedly attacked, resulting in over $4 million stolen from the Ethereum and Solana chains. According to MetaWin CEO Skel, the attacker exploited the platform's frictionless withdrawal system to breach MetaWin's hot wallet.
DeltaPrime
On November 11, 2024, the DeFi protocol DeltaPrime was attacked on Avalanche and Arbitrum, with initial loss estimates at $4.75 million. The root cause of the attack was a lack of input validation in the reward claiming feature.

(https://x.com/DeltaPrimeDefi/status/1855899502944903195)
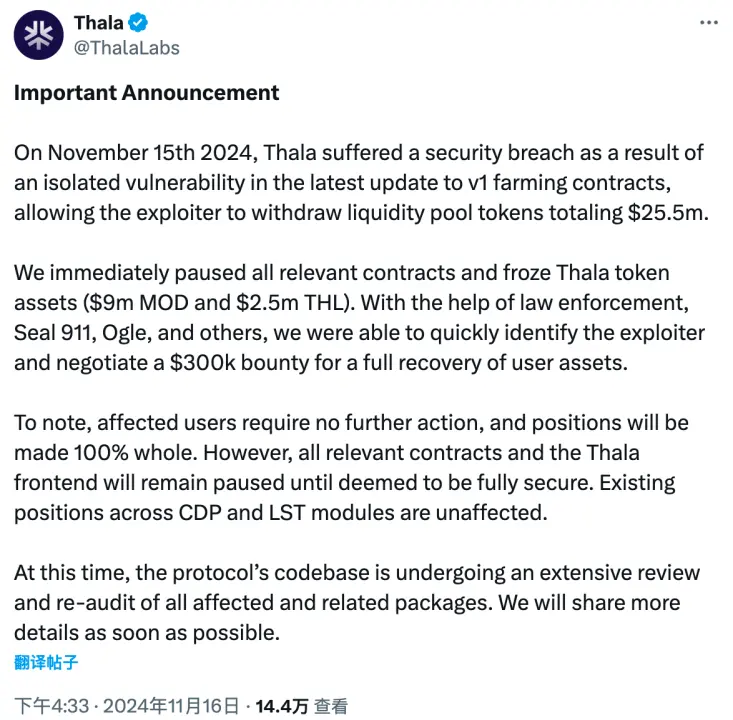
Thala
On November 15, 2024, the Aptos-based DeFi project Thala was attacked, resulting in $25.5 million stolen. The attacker exploited a vulnerability in its smart contract. The project team paused the relevant smart contracts and froze some tokens, successfully freezing about $11.5 million in assets. After collaborating with law enforcement and several blockchain security teams, the project team successfully negotiated to recover the assets, allowing the attacker to keep $300,000 as a bounty.
(https://x.com/thalalabs/status/1857703541089120541?s=46&t=bcMyidYO0QkS5ajIW9CBdg)
DEXX
On November 16, 2024, multiple users' funds were stolen from the on-chain trading terminal DEXX. According to the SlowMist Security Team, the loss from this incident has reached $21 million. Currently, the SlowMist Security Team is assisting DEXX officials and partners in ongoing analysis. On November 28, the SlowMist Security Team announced that they had collected 8,612 DEXX attacker addresses on the Solana chain, with EVM chain attacker addresses to be disclosed after the cleaning statistics are completed.

(https://x.com/MistTrackio/status/1862134946090881368)_
Polter Finance
On November 17, 2024, the Fantom-based DeFi project Polter Finance was attacked, resulting in losses of approximately $12 million. The attacker drained the BOO token reserves through a flash loan, artificially inflating the calculated price of BOO. This allowed them to borrow tokens far exceeding the actual value of the collateral, resulting in substantial profits. The platform's founder stated that they have reported the incident to Singapore authorities and attempted to contact the attacker through on-chain messages to negotiate the return of funds, but have not yet received a response.

(https://x.com/polterfinance/status/1857971122043551898)
Feature Analysis and Security Recommendations
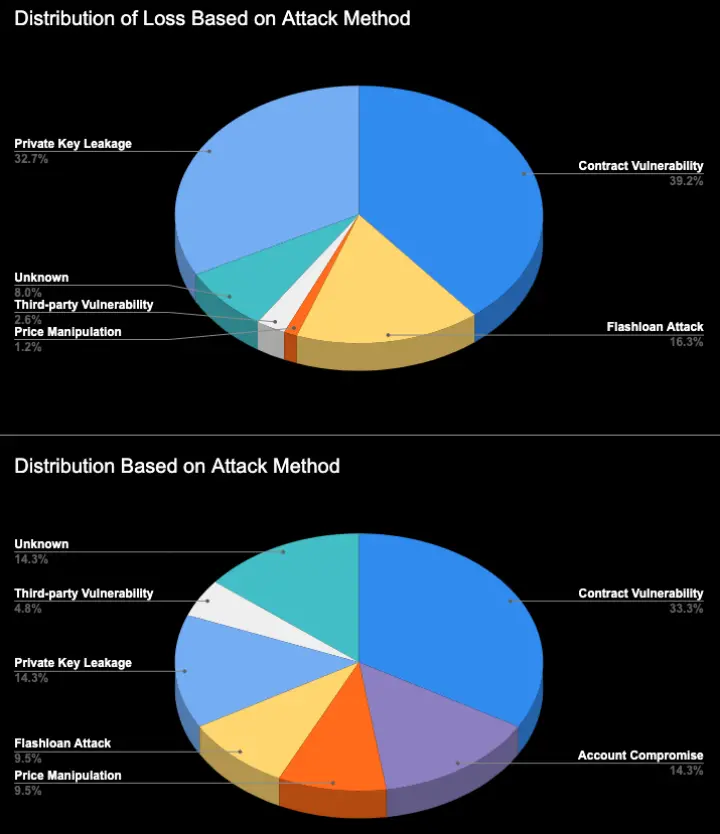
The number of security incidents and the scale of losses this month have significantly decreased compared to last month, reflecting ongoing improvements in the industry's security measures. Notably, contract vulnerabilities accounted for the highest proportion of incidents in terms of both distribution and losses. The seven contract vulnerability exploitation incidents this month caused approximately $30 million in losses, accounting for 39% of total losses. The SlowMist Security Team recommends that project teams remain vigilant and conduct regular comprehensive security audits, track and address new security threats and vulnerabilities, and protect project and asset security.
Additionally, the SlowMist Security Team noted that there were real cases of AI poisoning attacks targeting the crypto industry this month. This phenomenon indicates that the target range of supply chain attacks is further expanding. Some developers, in pursuit of efficiency, may overly rely on AI-generated code while neglecting the review of code security. Therefore, the SlowMist Security Team reminds developers and project teams not to blindly trust the output results when using AI-generated code. All code should undergo rigorous security audits and testing before being put into actual use to prevent security risks and protect the assets of projects and users. Meanwhile, project teams should strengthen the overall security management of the supply chain, conduct comprehensive assessments of third-party tools and services, and continuously monitor security dynamics in related fields to respond promptly to new threats.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




